back in my days, crypto does not mean blockchain#Cryptocurrency
enigma-machine
crypto-shangmi
crypto-pqc
crypto-pkcs
A Crash Course in Everything Cryptographic – Noteworthy - The Journal Blog ❗!important
Survival Guide - Encryption, Authentication, Digests, MAC and Signatures ❗!important
The Genius Math of Modern Encryption - YouTube
Category:Theory of cryptography - Wikipedia
Crypto Forum (cfrg) ❗!important, IETF
Limited Additional Mechanisms for PKIX and SMIME (lamps) ❗!important, IETF
Cryptology ePrint Archive ❗!important
C2SP/C2SP: Community Cryptography Specification Project maintains specs and test vectors
Welcome | Practical Cryptography for Developers
nakov/Practical-Cryptography-for-Developers-Book: Practical Cryptography for Developers: Hashes, MAC, Key Derivation, DHKE, Symmetric and Asymmetric Ciphers, Public Key Cryptosystems, RSA, Elliptic Curves, ECC, secp256k1, ECDH, ECIES, Digital Signatures, ECDSA, EdDSA
Cryptography 101 with Alfred Menezes – Video lectures, notes, and exercises in all areas of applied cryptography
Cryptography 101 - YouTube
The International Association for Cryptologic Research
IACR - YouTube
科普园地_国家密码管理局
密码学报 中国密码学会
中国密码学会 - 密评工作
Course
Cryptography | Computer science theory | Computing | Khan Academy
Cryptography I | Coursera
The Cryptopals Crypto Challenges
The Joy of Cryptography ❗!important, course
A Graduate Course in Applied Cryptography ❗!important, course
Crypto 101
ECE407/CS407: Cryptography
7 Cryptography Concepts EVERY Developer Should Know - YouTube
Secret Codes: A History of Cryptography (Part 1) - YouTube
More Secret Codes: A History of Cryptography (Part 2) - YouTube
In cryptography, these entities are usually used:
- Alice, Bob, Charles, Douglas: authentic users
- Eve: eavesdropper
- Mallory: MITM attacker
- Satan: malicious user/hacker
Education Center | Explore Now | Encryption Consulting
Classical Cryptography
Classical Cryptography - YouTube
The Unbreakable Kryptos Code - YouTube Vigenère cipher, substitution Cipher
Benchmarks
eBACS: ECRYPT Benchmarking of Cryptographic Systems
PQ Code Package Benchmarks
Symmetric Cryptography
Symmetric-key algorithm - Wikiwand
密码学学习笔记04对称加密 - 知乎
Block Ciphers
where input are segmented into blocks and the encrypted output are the same length as the input, contrast "stream ciphers"
Block cipher - Wikiwand
Lecture3 Lecture 3: Block Ciphers and the Data Encryption Standard
Anatomy of a password disaster – Adobe’s giant-sized cryptographic blunder – Naked Security study of Adobe's leaked password database
Feistel Cipher - Computerphile - YouTube
Modes of operation
Block cipher mode of operation - Wikiwand
Block ciphers, as the name suggests, encrypts blocks. The methods of segmenting data into blocks is called "modes of operation".
The Third NIST Workshop on Block Cipher Modes of Operation 2023 | CSRC
Modes of Operation - Computerphile - YouTube
ECB (Electronic codebook): simply divides a message into 16 byte blocks, preserves pattern (for experts only: ECB should never be used except in some very specific cases)
CBC (Cipher-block chaining): first block XORed with Initialization Vector (IV) (nonce), every other block XORed with the ciphertext of the block preceding it; however this introduces dependency on previous block and encryption cannot be parallelized
PCBC (Propagating cipher-block chaining): similar to CBC, but the plaintext is also XORed with the ciphertext for next round
CTR (Counter mode): uses counter and nonce (similar to IV) per block to allow each block to be encrypted concurrently
GCM (Galois/Counter Mode): authenticated encryption with associated data (AEAD), Galois MAC is computed and used for next round
CBC mode is suspectable to Padding oracle attack (Vaudenay Attack)
Moxie Marlinspike >> Blog >> The Cryptographic Doom Principle
Always Encrypt-then-MAC, so that verifying the MAC does not involve decryption
Counter mode transforms a block cipher into a stream cipher.
Authenticated encryption - Wikiwand GCM, CCM, protects against chosen ciphertext attack on decryption oracle
Authenticated Encryption in .NET with AES-GCM
DES
Even Triple DES (3-DES) is not recommended
Data Encryption Standard - Wikiwand
【计算机博物志】DES的生与死 - YouTube
AES
Advanced Encryption Standard - Wikiwand
Lecture 8: AES: The Advanced Encryption Standard
Protect your TCP tunnel by implementing AES encryption with Python [Tutorial] | Packt Hub
Crypto competitions: AES: the Advanced Encryption Standard
AES Explained (Advanced Encryption Standard) - Computerphile - YouTube
AES GCM (Advanced Encryption Standard in Galois Counter Mode) - Computerphile - YouTube
One Encryption Standard to Rule Them All! - Computerphile - YouTube
Almost All Web Encryption Works Like This (SP Networks) - Computerphile - YouTube
AES: How to Design Secure Encryption - YouTube
CTR mode, also known as Counter mode, is a stream cipher mode of AES encryption. With stream cipher encryption, it is not necessary to encrypt the plaintext in fixed blocks like AES in CBC mode, which encrypts data in 16-byte blocks. If the plaintext to be encrypted is smaller than the block size, padding is required to process a complete 16-byte block.
ARIA
RFC 5794 - A Description of the ARIA Encryption Algorithm
AES-256 vs ARIA-256 | Popular Encryption Standards Comparison
Commands
opessl openssl is for proof of concept
man enc # show ciphers
# encryption
openssl aes-256-cbc -in attack-plan.txt -out message.enc
# decryption
openssl aes-256-cbc -d -in message.enc -out plain-text.txt
# speed comparison
openssl speed -aes-256-cbc -aria-256-cbc# encryption
gpg --cipher-algo AES256 --symmetric filename.tar.gz
# decryption
gpg --output filename.tar.gz --decrypt filename.tar.gz.gpgStream Ciphers
Block Ciphers are more mature.
Some Block Ciphers in counter mode can be used as Stream Ciphers.
Chacha Cipher
alternative to AES
Chacha Cipher - Computerphile - YouTube
RFC 8439 - ChaCha20 and Poly1305 for IETF Protocols
ARX cipher: add, rotate, xor
The design of Chacha20 encryption
The design of Poly1305 MAC
Asymmetric Cryptography
Public-key cryptography - Wikiwand
Asymmetric Encryption: An Introduction To Asymmetric Cryptography
Public Key crypto simply works with numbers. This means that any messages would have to be converted into a number before being encrypted.
There are generally three things asymmetric algorithms can do:
- Encrypt/decrypt
- Sign/verify
- Key exchange
However, not all algorithms can perform all functions:
- RSA: Used for encryption, decryption, signing, and verifying.
- DSA: Used for signing and verifying.
- Diffie-Hellman: Used for key exchange.
- ECC: Used for signing and verifying (ECDSA), key exchange (ECDH), and encryption and decryption (EC ElGamal)
Backdoors in Asymmetric Cryptography
Why I don’t Trust NIST P-256 | Credelius
How to manipulate curve standards: a white paper for the black hat
How the NSA (may have) put a backdoor in RSA’s cryptography: A technical primer
NIST's P-256, P-384, P-521 curves are distrusted
Curve25519, Curve448 are used by the community (x25519 for ECDH, ed25519/EdDSA for signature)
RSA
RSA (cryptosystem) - Wikiwand
How does RSA work? – Hacker Noon
Understanding the RSA Algorithm: A Deep Dive into Asymmetric Cryptography
PKCS 1 - Wikiwand
RFC 8017 - PKCS #1: RSA Cryptography Specifications Version 2.2
RSA Signing is Not RSA Decryption optimal asymmetric encryption padding (OAEP) is used for pre/post-processing before RSA
Prime Numbers & RSA Encryption Algorithm - Computerphile - YouTube
Breaking RSA - Computerphile - YouTube
The RSA Encryption Algorithm (1 of 2: Computing an Example) - YouTube
The RSA Encryption Algorithm (2 of 2: Generating the Keys) - YouTube
How prime numbers protect your privacy #SoME2 - YouTube
-
Generate two large co-prime numbers, p and q.
-
Find n = pq and phi = (p-1) (q-1)
-
Select e such that 1 < e < phi, and e is coprime of phi
-
Find d, which is the multiplicative inverse of e modulo phi.
-
The couple (e, n) is the public key
-
The couple (d, n) is the private key
-
Ciphertext c = m^e mod n
-
Plaintext m = c^d mod n
-
RSA keypair is actually a trio of numbers
e,nanddrelated such thatm^de%n=m -
public key:
(e, n), private key:d -
s = h^d%n,s= signature,h= hash of messagem -
To verify, check if
s^e%nequalsh
Pretty Good Privacy (PGP) and Digital Signatures | Linux Journal
Elliptic Curve Cryptography (ECC)
ANSI X9.62-2005_317.pdf The Elliptic Curve Digital Signature Algorithm
FIPS 186-5, Digital Signature Standard (DSS) | CSRC P-192, P-256, P-384 curves
RFC 5639 - Elliptic Curve Cryptography (ECC) Brainpool Standard Curves and Curve Generation avoid potential patent issues associated other ECC curves
RFC 6979 - Deterministic Usage of the Digital Signature Algorithm (DSA) and Elliptic Curve Digital Signature Algorithm (ECDSA)
RFC 6605 - Elliptic Curve Digital Signature Algorithm (DSA) for DNSSEC
A (Relatively Easy To Understand) Primer on Elliptic Curve Cryptography
Elliptic Curve Cryptography: a gentle introduction - Andrea Corbellini
how does ECDSA works - Phind
Paul Miller — Learning fast elliptic-curve cryptography
ECDSA: Elliptic Curve Signatures | Practical Cryptography for Developers
EdDSA and Ed25519 | Practical Cryptography for Developers
Elliptic Curves over Finite Fields | By RareSkills – RareSkills basic ZKP
RFC 8032 - Edwards-Curve Digital Signature Algorithm (EdDSA)
EdDSA Keys and Signatures
Ed25519: high-speed high-security signatures highly efficient algo with strengh similar to RSA with ~3000-bit keys
A Deep dive into Ed25519 Signatures
ECDSA vs EdDSA - Sefik Ilkin Serengil EdDSA is more effient and secure than ECDSA
cryptography - SSH Key: Ed25519 vs RSA - Information Security Stack Exchange
age
Ciphertext indistinguishability
Ciphertext indistinguishability - Wikiwand
Chosen-plaintext attack - Wikiwand
Chosen-ciphertext attack - Wikiwand CCA
Adaptive chosen-ciphertext attack - Wikiwand
- indistinguishability under chosen plaintext attack (IND-CPA)
- indistinguishability under (non-adaptive) chosen ciphertext attack (IND-CCA1)
- indistinguishability under adaptive chosen ciphertext attack (IND-CCA2)
These are useful for proving the protocol is Universal Composable.
Universal composability - Wikiwand
Universally Composable Security: A New Paradigm for Cryptographic Protocols
encryption - What is universal composability guaranteeing, specifically? Where does it apply, and where does it not? - Cryptography Stack Exchange
Algorithms
Bit security measures the number of trials required to brute-force a key. 128 bit security means 2128 trials to break.
Cryptographic nonce - Wikiwand
Comparison of cryptography libraries - Wikiwand
Computer and Network Security by Avi Kak
Hashing/Key Derivation Function
Key derivation function - Wikiwand
HKDF - Wikiwand HMAC (keyed cryptographic hash functions) are candidates KDF
Cryptographic Extraction and Key Derivation: The HKDF Scheme
KEM Combiners secure pseudorandom function (PRF)
X-Wing IND-CCA KEM
On Robust Combiners for Oblivious Transfer and Other Primitives | SpringerLink
draft-irtf-cfrg-hybrid-kems-03 - Hybrid PQ/T Key Encapsulation Mechanisms hybrid KEM schemes, security considerations
Secure Hash Algorithms - Wikiwand SHA
SHA: Secure Hashing Algorithm - Computerphile - YouTube
SHA-1 - Wikiwand
FIPS 180-1, Secure Hash Standard | CSRC
SHA-2 - Wikiwand
FIPS 180-4, Secure Hash Standard (SHS) | CSRC
SHA2 Fatal Flaw? (Hash Length Extension Attack) - Computerphile - YouTube
Coding a SHA2 Length Extension Attack - Computerphile - YouTube
SHA-3 - Wikiwand Kaccak, SHAKE
FIPS 202, SHA-3 Standard: Permutation-Based Hash and Extendable-Output Functions | CSRC
SHAKE (Sponge Function) allows for hashing arbitrary length input and generating arbitrary length output
SHA-3, Keccak and SHAKE (Sponge Function) - YouTube
RFC 6194 - Security Considerations for the SHA-0 and SHA-1 Message-Digest Algorithms 💀 deprecated
RFC 6234 - US Secure Hash Algorithms (SHA and SHA-based HMAC and HKDF) SHA-2
RFC 5869 - HMAC-based Extract-and-Expand Key Derivation Function (HKDF)
RFC 7693 - The BLAKE2 Cryptographic Hash and Message Authentication Code (MAC)
RFC 4418 - UMAC: Message Authentication Code using Universal Hashing UHASH is very efficient on 32-bits CPU (embedded systems)
SP 800-56C Rev. 2, Recommendation for Key-Derivation Methods in Key-Establishment Schemes | CSRC
SP 800-108 Rev. 1, Recommendation for Key Derivation Using Pseudorandom Functions | CSRC
SP 800-227, Recommendations for Key-Encapsulation Mechanisms | CSRC
Key derivation function - Wikiwand
Key Derivation Functions vs. Password Hashing Schemes - Cryptography Stack Exchange
encryption - What is the difference between Key Derivation Function and (salted) Hash? - Information Security Stack Exchange
Storing password/Password hashing
the (password) hashing function should be relatively expensive to calculate in case of brute-force attacks
it takes a password, a salt, and a cost factor as inputs then generate a password hash for storage
How To Safely Store A Password | codahale.com bcrypt
Secure Salted Password Hashing - How to do it Properly
The difference between Encryption, Hashing and Salting
Best practices for password hashing and storage - draft-ietf-kitten-password-storage expired 2022-03-31
Serious Security: How to store your users’ passwords safely – Naked Security
How Dropbox securely stores your passwords | Dropbox Tech Blog
Salt (cryptography) - Wikiwand
cryptography - Do any security experts recommend bcrypt for password storage? - Information Security Stack Exchange
BCrypt Explained - DEV Community 👩💻👨💻
scrypt - Wikiwand
RFC 7914 - The scrypt Password-Based Key Derivation Function
bcrypt - Wikiwand
Bcrypt, a Popular Password Hashing Algorithm, Starts Its Long Goodbye | WIRED
PBKDF2 - Wikiwand
PBKDF2 Hashing Algorithm. Before moving into the PBKDF2 hashing… | by Nishothan Vettivel | Medium
PBKDF2 and Encrypting Data. What keeps your wireless access point… | by Prof Bill Buchanan OBE FRSE | Jan, 2025 | Medium
RFC 2898 - PKCS #5: Password-Based Cryptography Specification Version 2.0
lukeed/salteen: A snappy and lightweight (259B) utility to encrypt and decrypt values with salt.
multiformats/multihash: Self describing hashes - for future proofing
Argon2 - Wikiwand
P-H-C/phc-winner-argon2: The password hash Argon2, winner of PHC
How to enable Argon2 KDF in Bitwarden - gHacks Tech News
Authenticity
Hash vs. Message Authentication Code | Baeldung on Computer Science
MAC ~= hashing with shared key
less prune to replay attack
Message authentication code - Wikiwand MAC
Hash-based message authentication code - Wikiwand HMAC, hash with secret key
Moxie Marlinspike >> Blog >> The Cryptographic Doom Principle Encrypt-then-MAC
Mandatory Access Control
HMAC - Wikiwand
Securing Stream Ciphers (HMAC) - Computerphile - YouTube
RFC 2104 - HMAC: Keyed-Hashing for Message Authentication
If both encryption and authentication are required, consider authenticated encryption and authenticated encryption with associated data (AEAD), such as AES-GCM.
draft-irtf-cfrg-aead-limits-10 - Usage Limits on AEAD Algorithms
Digital Signatures: encrypt a known data (nonce or message hash) with sender's private key
Certificate Authorities: a trusted third party that will digitally sign and publish the public key bound to a user or entity
Implementation
Implementation
Most TLS library provides crypto layer
openssl
openssl#Alternate Implementations
The Linux Crypto API for user applications
This is slower than OpenSSL
Noise Protocol Framework
The Noise Protocol Framework
Welcome to pyca/cryptography — Cryptography documentation
pyca/cryptography: cryptography is a package designed to expose cryptographic primitives and recipes to Python developers.
NaCl
Introduction | libsodium
jedisct1/libsodium: A modern, portable, easy to use crypto library.
PyNaCl: Python binding to the libsodium library — PyNaCl documentation
pyca/pynacl: Python binding to the Networking and Cryptography (NaCl) library
cryptlib Encryption Toolkit
cryptlib/cryptlib: cryptlib security toolkit
Welcome to PyCryptodome’s documentation pycryptodome provides Crypto package (to replace PyCrypto), pycryptodomex provides Cryptodome package
Legrandin/pycryptodome: A self-contained cryptographic library for Python
AES instruction set - Wikiwand
Key Exchange
Key Exchange Problems - Computerphile - YouTube
RFC 9142 - Key Exchange (KEX) Method Updates and Recommendations for Secure Shell (SSH)
End to End Encryption (E2EE) - Computerphile - YouTube
How Signal Instant Messaging Protocol Works (& WhatsApp etc) - Computerphile - YouTube
SP 800-56A Rev. 3, Recommendation for Pair-Wise Key-Establishment Schemes Using Discrete Logarithm Cryptography | CSRC
SP 800-56B Rev. 2, Recommendation for Pair-Wise Key-Establishment Using Integer Factorization Cryptography | CSRC
Non-Interactive Key Exchange (NIKE)
no challenges are presented to be validated
Random oracle - Wikiwand
Understanding Non-Interactive Key Exchange in Cryptography !🔐🌐 | by Samuel Guxegdsa | Medium only sends a single, asynchronous message from each party
Non-Interactive Key Exchange | SpringerLink
Non-Interactive Key Exchange
Cryptographic algorithms as interactive and non-interactive proofs | by Filza | Xord | Medium
Diffie–Hellman key exchange
Diffie–Hellman key exchange - Wikiwand
Elliptic-curve Diffie–Hellman - Wikiwand
Implementation of Diffie-Hellman Algorithm - GeeksforGeeks
Unraveling the Diffie-Hellman Key Exchange: A Foundation of Modern Cryptography
Traditional DH:
- one party choose and announce
g,p - party A choose secret
aand announce public keyA = g^a mod p - party B choose secret
band announce publicB = g^b mod p - party A compute
B^a mod p, party B computeA^b mod p - the number should be the same (note
B^a = A^b = g^abinmod pgroup) and can be used as session key (or pre-master key)
ECDH:
- party A choose secret key
d_a, public keyH_aon Elliptic-curve with base pointG - party B choose secret key
d_b, public keyH_bon Elliptic-curve with the same base pointG - the public keys
H_aandH_bare announced - party A compute
d_a*H_b, party B computed_b*H_a, - the number should be the same (note
d_a*H_b = d_a*(d_b*G) = d_b*(d_a*G) = d_b*H_a) and can be used as session key (or pre-master key)
PKCS #3: Diffie-Hellman Key-Agreement Standard
Intro to PKCS #3: Diffie-Hellman Key Agreement Standard – wolfSSL
RFC 2631 - Diffie-Hellman Key Agreement Method
RFC 7919 - Negotiated Finite Field Diffie-Hellman Ephemeral Parameters for Transport Layer Security (TLS)
RFC 8422 - Elliptic Curve Cryptography (ECC) Cipher Suites for Transport Layer Security (TLS) Versions 1.2 and Earlier
Secret Key Exchange (Diffie-Hellman) - Computerphile - YouTube
Diffie Hellman -the Mathematics bit- Computerphile - YouTube
Diffie-Hellman Key Exchange: How to Share a Secret - YouTube
Double Ratchet Messaging Encryption - Computerphile - YouTube Extended Triple Diffie–Hellman (X3DH)
Signal >> Specifications >> The X3DH Key Agreement Protocol
Signal's protocol, requires identity key
Post-Quantum Extended Diffie–Hellman - Wikiwand
Cryspen | An Analysis of Signal's PQXDH
[2501.09568] Quantum Diffie-Hellman key exchange Quantum system
Internet Key Exchange (IKE)
used by many technologies that are protected by IPsec, e.g. VPN, SFTP, SSH and Point-to-Point Protocol (PPP).
IPsec - Wikiwand
Internet Key Exchange - Wikiwand
What is Internet Key Exchange (IKE) and How Does It Work? | Definition from TechTarget
what is Internet Key Exchange Protocol Version 2 (IKEv2)? - Phind
RFC 4306 - Internet Key Exchange (IKEv2) Protocol
RFC 4754 - IKE and IKEv2 Authentication Using the Elliptic Curve Digital Signature Algorithm (ECDSA)
Internet Key Exchange Version 2 (IKEv2) Parameters
Attribute-Based Encryption
A Gentle Introduction to Attribute-Based Encryption
Signature
What are Digital Signatures? - Computerphile - YouTube
RSA and Digital Signatures - GeeksforGeeks
Digital Signature Algorithm (DSA) - GeeksforGeeks
Blockchain - Elliptic Curve Digital Signature Algorithm (ECDSA) - GeeksforGeeks
Complexity of ECDSA is not deterministic
#RSA
#Elliptic Curve Cryptography (ECC)
BLS
BLS digital signature - Wikiwand
BLS Signature for Busy People
Crypto Pills #11: BLS Signatures. BLS (Boneh–Lynn–Shacham) signatures… | by Guilherme Balena Versiani | Medium
Steganography
Steganography - Wikiwand
隐写术鉴赏 - YouTube
Outguess – Rbcafe
OutGuess - Wikiwand
resurrecting-open-source-projects/outguess: Universal steganographic tool
StegCloak
KuroLabs/stegcloak: Hide secrets with invisible characters in plain text securely using passwords 🧙🏻♂️⭐
How to Hide Secrets in Strings— Modern Text hiding in JavaScript | by Mohan Sundar | Bits and Pieces
resurrecting-open-source-projects/outguess: Universal steganographic tool
Homomorphic Encryption
ciphertext that can be processed or analyzed
Homomorphic encryption - Wikiwand
Fully Homomorphic Encryption | We are a community of researchers and developers interested in advancing homomorphic encryption and other secure computation techniques.
Fully Homomorphic Encryption | Resources ❗!important
[2503.05136] The Beginner's Textbook for Fully Homomorphic Encryption
The Beginner’s Textbook for Fully Homomorphic Encryption online version
Homomorphic Encryption: How It Works | Splunk
What Is Homomorphic Encryption?
3 Homomorphic Encryption Trends for 2025
How a 7-Year-Old Can Understand FHE / Fully Homomorphic Encryption | by Nothing Research | Medium
Advanced FHE Protocols for the Blockchain (RWC 2024) - YouTube
Homomorphic Encryption vs Zero Knowledge
Fully Homomorphic Encryption and Zero Knowledge: Data security secrets | by Illy’s Web3 blog | Medium
FHE Vs ZK Vs MPC, what are the differences between the three encryption technologies? | Odaily星球日报 on Binance Square
Privacy
Privacy-Preserving Data Science, Explained – OpenMined
crypt.fyi - Open-Source Zero-Knowledge Post-Quantum End-to-End Encrypted One-Time Secret Sharing
Zero-Knowledge sharing
Lattice-based_Zero-knowledge_Proofs_for_Blockchain_Confidential_Transactions.pdf
Zero-knowledge proof/ZKP
Zero-knowledge proof - Wikiwand
把問題和答案的關聯轉變成機率問題, 透過趨近無窮次的試驗,使猜對的機率趨近 0
Non-interactive zero-knowledge proof - Wikiwand
Introduction | ZKDocs
trailofbits/zkdocs: Interactive documentation on zero-knowledge proof systems and related primitives.
Zero-Knowledge Proofs: A Beginner's Guide
Zero Knowledge Proofs: An illustrated primer – A Few Thoughts on Cryptographic Engineering
Zero-knowledge proofs explained in 3 examples
What are Zero Knowledge Proofs? – OpenMined
Zero-knowledge Proof: IZKs, NIZKs, SNARKS, STARKS Explained. | by Mayowa Olatunji (@web3MIO) | Coinmonks | Medium
Full Guide to Understanding zk-SNARKs and zk-STARKS
I can prove I’ve solved this Sudoku without revealing it - YouTube
Zero Knowledge Proofs: A Technical Deep Dive - YouTube
Zero Knowledge Proofs - YouTube
神奇的零知识证明!既能保守秘密,又让别人信你! - YouTube
The Magic of Zero-Knowledge Proofs #SoME3 - YouTube
- zk-SNARKs (Succinct Non-Interactive Argument of Knowledge)
- zk-STARKs (Scalable Transparent ARguments of Knowledge)
- Bulletproofs
- Folding Schemes
- Lookup
Leveraging Verifiable Credentials and Zero Knowledge Proofs with Sindri GSP1302 - YouTube
Zero Knowledge Selective Disclosure (ZK-SD-VCs) | IOTA Documentation
General-Purpose Zero-Knowledge Proofs for Verifiable Credentials PDF
rwot9-prague/topics-and-advance-readings/verifiable-credentials-and-zero-knowledge-proof-systems.md at master · WebOfTrustInfo/rwot9-prague
ZK Math Explained: Homomorphisms
ZK Math Explained: Understanding Elliptic Curves
ZK Math Explained: The Elliptic Curve Discrete Logarithm Problem
ZPK uses different signatures
Short Randomizable Signatures "PS" signature
Zhiyi-Zhang/PS-Signature-and-EL-PASSO: A C++ Implementation of Short Randomizable Signatures (PS Signatures) and EL PASSO (Privacy-preserving, Asynchronous Single Sign-On)
Practical Post-Quantum Signatures for Privacy
Signatures with efficient protocols Camenisch-Lysyanskaya signature (CL signature), obsolete, signature size linear to message size
LaZer: a Lattice Library for Zero-Knowledge and Succinct Proofs (RWC 2024) - YouTube
Zero-Knowledge Proofs: How it Works & Use Cases in 2026
Zero-Knowledge Proof (ZKP) — Explained | Chainlink
Zero-Knowledge Proof: Applications & Use Cases - Chainlink
(PDF) Zero-knowledge proof framework for privacy-preserving financial compliance
BBS Signatures
Boneh-Boyen-Shacham signatures
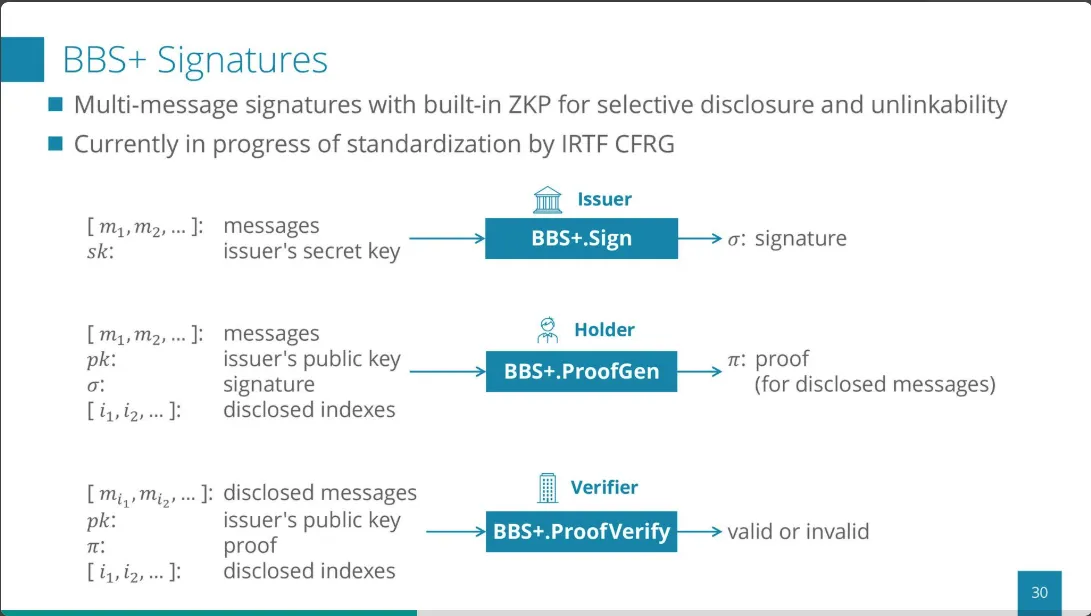
- multi-message signatures with built-in ZKP for selective disclosure and unlinkability
- requires an array of scaler -> Termwise encoding of claims
draft-irtf-cfrg-bbs-signatures - The BBS Signature Scheme
decentralized-identity/bbs-signature: The BBS Signature Scheme used for W3C SD
Anonymous Attestation Using the Strong Diffie Hellman Assumption Revisited
jsonld-signatures-bbs/sample at master · mattrglobal/jsonld-signatures-bbs
Intro to ZKPs using BBS+ signatures - YouTube
BBS+ Signatures – Part 2 - YouTube
zk-SNARKs
Non-interactive zero-knowledge proof - Wikiwand
snark-credentials/whitepaper.pdf at master · decentralized-identity/snark-credentials
scipr-lab/libsnark: C++ library for zkSNARKs
OpenMined/PyZPK: Python wrapper for open source Zero Proof Knowledge Library
zk-creds: Flexible Anonymous Credentials from zkSNARKs and Existing Identity... (RWC 2024) - YouTube
zkVMs
The Evolution of Rust inside zkVMs - Erik Kadena | RISC Zero - YouTube
Zeroing into zkVMs
zkTLS
zkTLS: Building A Verifiable and Private Web
Reclaim Protocol - Cryptographic Verification for Identity, Education, Employment & Travel whitepaper Security Analysis
Nascent.xyz | Crypto’s AirTag Moment: Unlocking Mass Adoption with Web Proofs